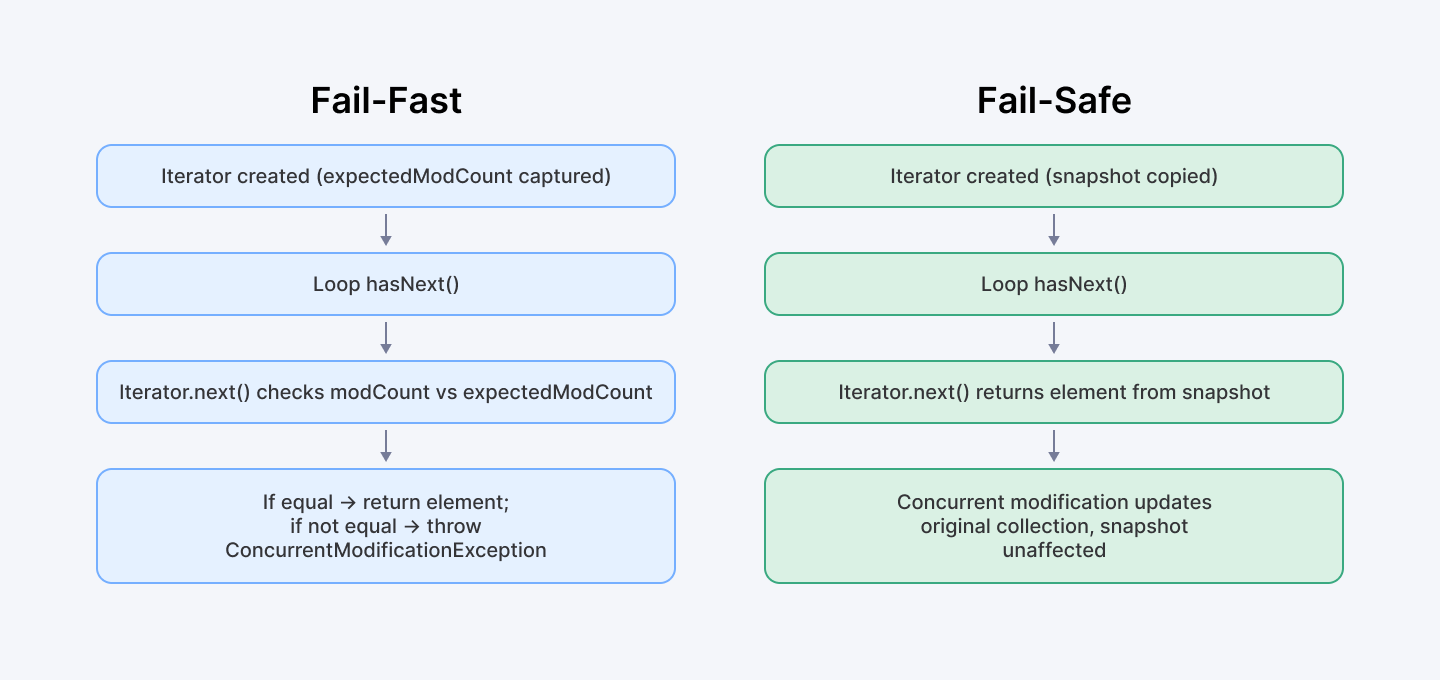
When working with Java collections, you'll encounter two primary iterator strategies: fail-fast and fail-safe. Each has distinct behaviors when handling concurrent modifications during collection traversal, affecting your application's reliability and performance.
Fail-fast iterators (used by ArrayList, HashSet, LinkedList, etc.) immediately detect structural modifications through an internal counter mechanism and throw a ConcurrentModificationException. In contrast, fail-safe iterators (provided by CopyOnWriteArrayList and ConcurrentHashMap) work on a snapshot of the data, preventing exceptions at the cost of potential consistency trade-offs.
In this guide, we'll explore the technical underpinnings of both iterator types with optimized, production-ready code examples. You'll learn exactly when to choose one over the other to build robust, concurrent Java applications.
Ready to build robust Java apps? Join Index.dev to connect with global teams, build cutting-edge apps, and grow your remote developer career!
Technical Anatomy of Fail‑Fast Iterators
Fail-fast iterators operate directly on the live collection and throw a ConcurrentModificationException when they detect structural changes. Let's explore how they work under the hood.
Mechanism and Implementation
Collections like ArrayList and LinkedList inherit a protected modCount field (from AbstractList) that increments with every structural modification. The iterator captures this value at creation time and verifies it hasn't changed during traversal.
- Guarantees: Best‑effort; not suitable as a synchronization mechanism.
- Performance: O(1) per iteration, minimal memory overhead—but unsafe under concurrent writes.
Here's an optimized example demonstrating fail-fast behavior:
Code Example: ArrayList Fail‑Fast
List<String> list = new ArrayList<>(List.of("A", "B", "C"));
import java.util.ArrayList;
import java.util.Iterator;
import java.util.List;
public class FailFastExample {
public static void main(String[] args) {
// Create a list with initial elements
List<String> list = new ArrayList<>(List.of("A", "B", "C"));
try {
// Get an iterator - internally captures current modCount value
Iterator<String> iterator = list.iterator();
while (iterator.hasNext()) {
String element = iterator.next();
System.out.println("Processing: " + element);
// Attempting a structural modification during iteration
if ("B".equals(element)) {
System.out.println("Adding element D to the list");
list.add("D"); // This modifies the underlying collection
}
}
} catch (Exception e) {
System.out.println("Exception caught: " + e.getClass().getSimpleName());
System.out.println("Message: " + e.getMessage());
}
System.out.println("Final list content: " + list);
}
}How It Works
- When we create the iterator with list.iterator(), it captures the current modCount value (let's say it's 0) as its expectedModCount.
- During the first call to next(), the iterator checks if modCount == expectedModCount (both 0), which passes.
- When we add "D" to the list with list.add("D"), the collection's modCount increments to 1.
- On the next iteration, when next() is called, the iterator's checkForComodification() method sees that modCount (1) doesn't equal expectedModCount (0) and throws a ConcurrentModificationException.
This mechanism provides immediate notification of concurrent modifications, making it excellent for detecting programming errors but unsuitable for multi-threaded scenarios without proper synchronization.
Also Check Out: DAO and DTO in Java | Key Concepts and Usage
Technical Anatomy of Fail‑Safe Iterators
Fail-safe iterators work on a snapshot or weakly-consistent view of the collection, ensuring they never throw a ConcurrentModificationException. Let's examine two primary implementations.
- CopyOnWriteArrayList: On each mutation, a new array is created. Iterators hold the old array reference, providing a stable snapshot. Great for read‑heavy workloads; expensive for writes (O(n) per update).
- ConcurrentHashMap: Iterators are weakly consistent—they reflect the state at or since iterator creation, may skip some updates, but never fail. Reads and writes proceed concurrently without locks on traversal.
Code Example: CopyOnWriteArrayList Fail‑Safe
import java.util.List;
import java.util.concurrent.CopyOnWriteArrayList;
public class CopyOnWriteArrayListExample {
public static void main(String[] args) {
// Create a CopyOnWriteArrayList with initial elements
CopyOnWriteArrayList<String> cowList =
new CopyOnWriteArrayList<>(List.of("X", "Y", "Z"));
System.out.println("Starting iteration...");
// This for-each loop uses the iterator internally
for (String element : cowList) {
System.out.println("Processing: " + element);
// This modification won't affect the current iteration
if ("Y".equals(element)) {
System.out.println("Adding element W to the list");
cowList.add("W"); // Creates a new internal array
}
}
System.out.println("Final list content: " + cowList);
System.out.println("List size: " + cowList.size());
}
}How CopyOnWriteArrayList Works
- CopyOnWriteArrayList creates a snapshot of its internal array when you call iterator().
- When we add "W" to the list with cowList.add("W"), the collection creates an entirely new array with the added element.
- However, our iterator continues to work on the original array snapshot it captured at creation time.
- This approach ensures that modifications during iteration don't affect the iterator's view, preventing ConcurrentModificationException.
This implementation provides thread safety without external synchronization but at the cost of potentially higher memory usage and stale data during iteration.
Code Example: ConcurrentHashMap Weakly‑Consistent
import java.util.Map;
import java.util.concurrent.ConcurrentHashMap;
public class ConcurrentHashMapExample {
public static void main(String[] args) {
// Create a ConcurrentHashMap with initial elements
ConcurrentHashMap<String, Integer> map = new ConcurrentHashMap<>();
map.put("apple", 1);
map.put("banana", 2);
System.out.println("Starting keySet iteration...");
// Using weakly consistent iterator through keySet()
for (String key : map.keySet()) {
System.out.println("Key: " + key + ", Value: " + map.get(key));
// This modification may or may not be visible during iteration
if ("apple".equals(key)) {
System.out.println("Adding cherry to the map");
map.put("cherry", 3);
}
}
System.out.println("Final map content: " + map);
}
}How ConcurrentHashMap's Iterator Works
Unlike CopyOnWriteArrayList, ConcurrentHashMap doesn't create a full copy. Instead, it offers a weakly consistent view:
- The iterator reflects the state of the map at the point of creation.
- It may or may not show modifications made after iterator creation.
- It never throws ConcurrentModificationException, even when the map is modified during iteration.
This approach balances consistency with performance, making it suitable for highly concurrent read/write scenarios.
Custom Fail‑Safe Implementation with Optimization
When you need a middle ground between full array copying and fail-fast behavior, you can implement a custom solution using read-write locks. Here's an optimized implementation:
import java.util.ArrayList;
import java.util.Iterator;
import java.util.List;
import java.util.concurrent.locks.ReentrantReadWriteLock;
public class CustomFailSafeList<T> implements Iterable<T> {
private final List<T> list = new ArrayList<>();
private final ReentrantReadWriteLock lock = new ReentrantReadWriteLock();
/**
* Adds an element to the list with write lock protection
*/
public void add(T element) {
lock.writeLock().lock();
try {
list.add(element);
} finally {
lock.writeLock().unlock();
}
}
/**
* Removes an element from the list with write lock protection
*/
public boolean remove(T element) {
lock.writeLock().lock();
try {
return list.remove(element);
} finally {
lock.writeLock().unlock();
}
}
/**
* Gets the size of the list with read lock protection
*/
public int size() {
lock.readLock().lock();
try {
return list.size();
} finally {
lock.readLock().unlock();
}
}
/**
* Creates a fail-safe iterator by taking a snapshot under a read lock
*/
@Override
public Iterator<T> iterator() {
lock.readLock().lock();
try {
// Create a snapshot while holding the read lock
return new ArrayList<>(list).iterator();
} finally {
lock.readLock().unlock();
}
}
/**
* Returns the list contents as a string
*/
@Override
public String toString() {
lock.readLock().lock();
try {
return list.toString();
} finally {
lock.readLock().unlock();
}
}
/**
* Usage example
*/
public static void main(String[] args) {
CustomFailSafeList<String> customList = new CustomFailSafeList<>();
customList.add("One");
customList.add("Two");
customList.add("Three");
System.out.println("Starting iteration...");
// Safe iteration with concurrent modification
for (String item : customList) {
System.out.println("Item: " + item);
if ("Two".equals(item)) {
customList.add("Four");
System.out.println("Added 'Four' during iteration");
}
}
System.out.println("Final list: " + customList);
System.out.println("List size: " + customList.size());
}
}How Our Custom Implementation Works
Our CustomFailSafeList provides thread-safe operations while optimizing memory usage:
- Write Operations: The add() and remove() methods acquire an exclusive write lock, ensuring only one thread can modify the list at a time.
- Read Operations: Methods like size() and toString() use a shared read lock, allowing multiple reads to occur concurrently.
- Iterator Creation: The crucial part is the iterator() method, which:
- Acquires a read lock (allowing other readers but blocking writers)
- Creates a snapshot copy of the current list
- Releases the lock before returning the iterator
This approach:
- Provides thread safety through read-write locking
- Creates snapshots only when needed (per iterator creation)
- Ensures modifications won't affect ongoing iterations
- Avoids the need for synchronizing the actual iteration process
The implementation balances safety and performance by using fine-grained locking and minimal copying, making it suitable for scenarios where CopyOnWriteArrayList would be too memory-intensive but thread safety is still required.
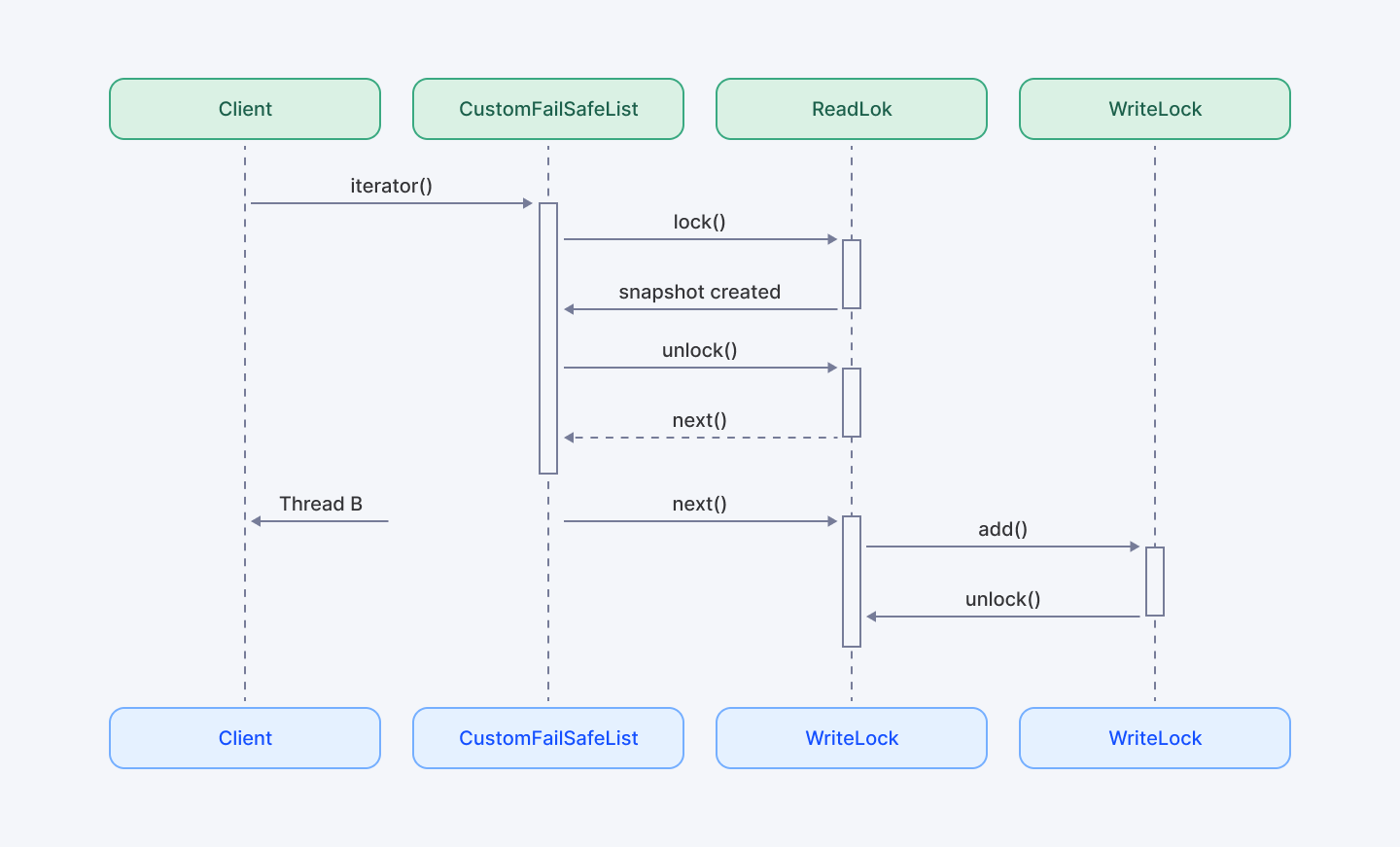
The UML sequence diagram above illustrates how our CustomFailSafeList ensures safe iteration in a concurrent environment by creating a snapshot under a read lock and isolating future mutations.
Best Practices and Use Cases
When choosing between fail-fast and fail-safe iterators, consider these guidelines:
When to Use Fail-Fast Iterators
- Single-threaded environments where you want immediate detection of unexpected modifications
- Debugging scenarios to identify and fix concurrent modification issues
- Performance-critical applications where the overhead of copying collections should be avoided
- When strict consistency is required during iteration
When to Use Fail-Safe Iterators
- Multi-threaded environments where collections may be modified concurrently
- Read-heavy workloads with occasional writes
- When exceptions during iteration would be problematic
- When slightly stale data during iteration is acceptable
When to Use Custom Implementations
- When you need fine-grained control over locking behavior
- Memory-constrained environments where full copies are too expensive
- Mixed read/write workloads where standard concurrent collections don't provide optimal performance
2025 Market Context and Trends
- Cloud‑Native & Microservices: With ~90% of enterprises adopting cloud‑native patterns by 2025, mutable state often lives in shared, distributed caches—making fail‑safe iterators indispensable for read‑heavy services.
- Real‑Time Big Data: Event‑driven pipelines (e.g., Apache Kafka consumers) benefit from weakly‑consistent, fail‑safe iteration to avoid blocking under high throughput.
- JVM Enhancements: Recent JDK releases (21+) optimize CopyOnWriteArrayList with reduced copy‑on‑write overhead and improved garbage‑collection behavior, narrowing the performance gap.
Performance and Memory Considerations
Each iterator strategy comes with performance trade-offs:
Fail-Fast (ArrayList, HashSet, etc.)
- ✅ Low memory footprint (no copying)
- ✅ Fast iteration (direct access)
- ❌ Requires external synchronization for thread safety
- ❌ Throws exceptions on concurrent modification
Fail-Safe (CopyOnWriteArrayList)
- ✅ Thread-safe without external synchronization
- ✅ Never throws ConcurrentModificationException
- ❌ Higher memory usage (full copy on every write)
- ❌ O(n) cost for every write operation
- ❌ Iteration may work on stale data
Fail-Safe (ConcurrentHashMap)
- ✅ Thread-safe with high concurrency
- ✅ Good performance for mixed read/write workloads
- ✅ No full copy required
- ❌ Weakly consistent views (may miss updates)
Custom Implementation
- ✅ Controlled memory usage (snapshots only when needed)
- ✅ Configurable trade-offs between safety and performance
- ❌ More complex to implement correctly
- ❌ Potential for lock contention under high concurrency
Security and Robustness Considerations
Improper iterator choice can lead to race conditions, data corruption, or even exploitation in high‑risk applications. A recent OpenJDK advisory (April 15, 2025) highlighted a potential Denial‑of‑Service vector when aggressive mutation patterns led to unbounded memory growth in CopyOnWriteArrayList under certain load. Always profile and test under realistic concurrency.
Read More: Getting Started with Async in Java Repositories
Conclusion
The right iterator strategy depends on your application's concurrency model, consistency needs, and performance constraints. After diving into the mechanisms of both approaches, you can see that each serves different scenarios in modern Java development.
Fail-fast iterators excel at catching bugs early through immediate exception throwing but require proper synchronization when multiple threads are involved. Fail-safe iterators handle concurrent modifications gracefully through snapshots or weak consistency models, though they may trade perfect consistency for stability.
When standard collections don't hit the sweet spot, custom implementations like our read-write lock example can provide a tailored balance between safety, memory usage, and performance.
Remember that there's no silver bullet—your architecture, workload patterns, and specific requirements should guide your choice between these powerful iteration strategies.
For Developers: Take your Java concurrency skills to the next level with in‑depth tutorials, code samples, and advanced patterns. Join Index.dev to match with top remote opportunities globally.
For Companies: Hire expert Java developers in 48 hours. Index.dev connects you with elite, vetted talent—backed by a 30-day risk-free trial. Start scaling today.